Access SSO User Info
In ToolJet, you can now pass user-specific authentication details from the SSO provider to connected datasources. This allows each user to access systems like Snowflake, Salesforce, GraphQL, and more using their own credentials, eliminating the need for shared logins. It ensures that enterprise security policies such as role-based access and row-level restrictions are enforced based on the user’s identity.
Accessing SSO User Info in App Builder
ToolJet exposes a global variable called ssoUserInfo within the App Builder, which contains user-specific authentication details from the active SSO session. This allows you to securely pass identity information, such as tokens and user identifiers into queries and logic within your app.
You can reference ssoUserInfo directly in queries or components to dynamically control access, personalize content, or forward authentication tokens to connected datasources that support OAuth 2.0 or OIDC.
Use the following syntax to refer to any exposed variable from ssoUserInfo:
{{globals.currentUser.ssoUserInfo.<variable-name>}}
Commonly Exposed SSO Variables
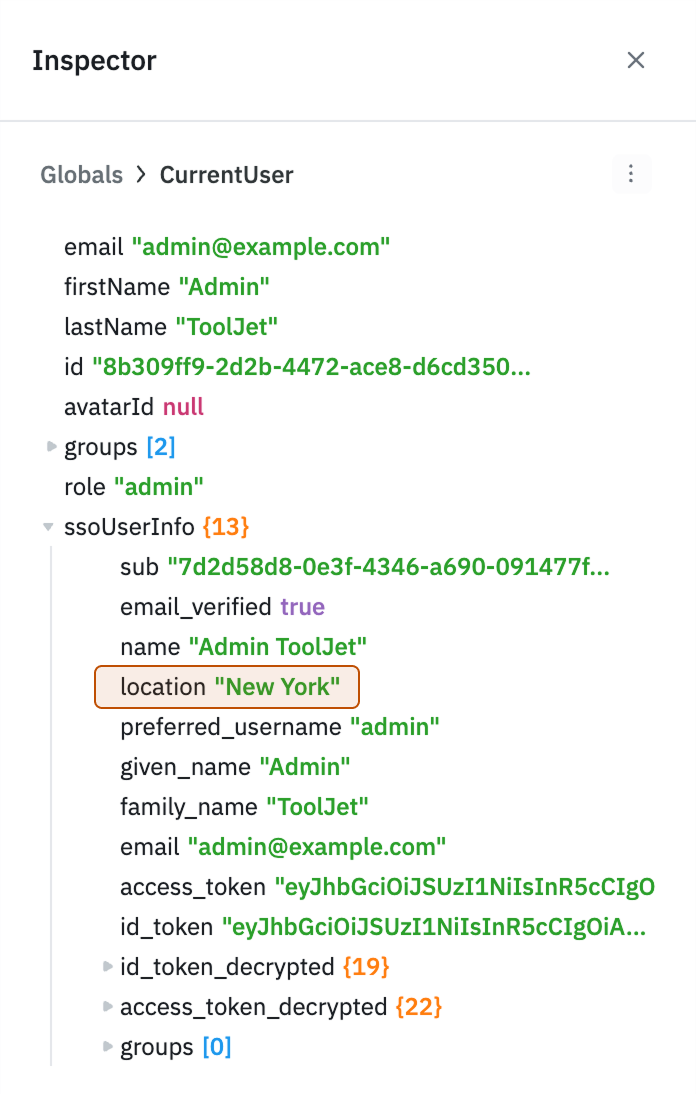
The exposed variables may vary depending on the identity provider. You can view all available variables in the Inspector panel under globals > currentUser > ssoUserInfo. Below are some commonly exposed variables:
| Variable | Description |
|---|---|
sub | Unique identifier for the user assigned by the identity provider. |
name | Full name of the authenticated user. |
given_name | User’s first name or given name. |
family_name | User’s last name or family name. |
picture | URL of the user’s profile picture. |
email | Email address associated with the user’s SSO identity. |
email_verified | Boolean flag indicating whether the email address has been verified. |
hd | Hosted domain or organization the user belongs to. |
access_token | OAuth 2.0 access token for the current user session, used to authenticate requests to connected datasources. |
id_token | Encoded ID token containing user identity claims in JWT format. |
id_token_decrypted | Decrypted contents of the ID token, useful for accessing detailed user claims. |
Automatic Token Refresh and ssoUserInfo Freshness
ToolJet automatically refreshes your OIDC access token in the background when it is near expiry, keeping your session active without requiring a page reload or re-login.
How It Works
ToolJet automatically refreshes your OIDC access token in the background when it expires, keeping your session active and ssoUserInfo up to date without a page reload.
If the refresh fails, your session will be invalidated.
Binding Recommendations
Depending on your use case, choose the binding pattern that best suits your needs:
| Binding | Behavior |
|---|---|
{{globals.currentUser.ssoUserInfo.<variable>}} | May briefly reflect stale values immediately after a token refresh; auto-syncs shortly after |
{{globals.server.currentUser.ssoUserInfo.<variable>}} | Always reflects the latest values; recommended for token-sensitive queries and datasource authentication |
For use cases where you are passing access_token or other credentials directly to a connected datasource, prefer globals.server.currentUser.ssoUserInfo to ensure the most up-to-date token is always used.
Custom SSO Variables (OIDC Claims)
ToolJet allows you to use custom SSO variables provided by your Identity Provider (IdP) during login.
Any custom claims (such as branch, location, or department) that are configured in your IdP and included in the authentication response will be available in ToolJet after successful login.
These claims can be accessed within the App Builder using:
{{globals.currentUser.ssoUserInfo.<claim_name>}}
Custom attributes must be explicitly configured in the Identity Provider to be included in the OIDC token or UserInfo response.